GFI MailSecurity – Review of a mature product for Microsoft Exchange
Recently I had to work with GFI MailSecurity and my first thought is -> A Mature product and a must have for all organization’s running MS Exchange
With the majority of email sent to users being spam or infected by malware, system administrators need every defense they can muster to protect their systems and their users. Best practices for any mail infrastructure comprise scanning inbound mail for content including inappropriate material, malicious scripts and infected attachments. It’s not enough just to do anti-spam checks like DNS blacklists and keyword scans; you need to check the message, any embedded scripts or HTML content, and any attachments for malicious content. Think defense in depth – multiple overlapping layers of security to protect your users and your data.
In the fight against malware and other malicious content, GFI MailSecurity is like a Patriot Missile battery – always on guard and protecting your infrastructure. GFI MailSecurity runs on current Windows server platforms and is intended to protect Microsoft Exchange and Lotus Domino deployments, but because it sits on top of Microsoft’s SMTP engine, it can protect any internal mail system by acting as the Internet MTA. GFI MailSecurity can be purchased alone, or bundled with GFI MailEssentials to provide anti-spam protection as well. GFI MailSecurity offers several key features including malware scanning of messages and attachments with multiple engines, link scanning, script removal, robust reporting, and easy administration. Let’s take a look at what is required to run this product.
System requirements
GFI MailSecurity runs on all current Windows server platforms (32 and 64bit, physical or virtual) which can be on the domain or in workgroup mode. It does require Microsoft Message Queuing, IIS, ASP.NET and Windows Authentication, along with an SMTP service. For purposes of this article, we’re going to install GFI MailSecurity on a bastion Windows 2008 host as an SMTP relay in our DMZ. To make sure all the prerequisites are installed, we can open an administrative cmd prompt and run this command (wraps for formatting, run this as a single line.)
>servermanagercmd -i as-msmq-activation web-server web-asp-net
web-windows-auth web-metabase web-lgcy-mgmt-console rsat-smtp smtp-server
That will install all the prerequisites.
Installing
Installation is fairly straightforward, requiring only few confirmations. After the standard fare, including accepting the EULA and checking for updates, the only really significant choice you will make merely comes up if you are installing on a server running multiple websites, where you must choose which site will host the administrative console. 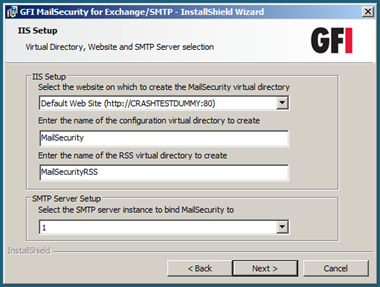
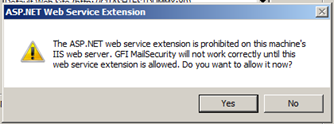
If you installed the prerequisites as advised earlier in this post, but did not configure IIS, you will be prompted to enable ASP.NET.
You will also be prompted to confirm the existing SMTP domains, and that services will be restarted as part of the installation. Click through that and a few moments later the product is installed. A reboot is not required.
Configuration
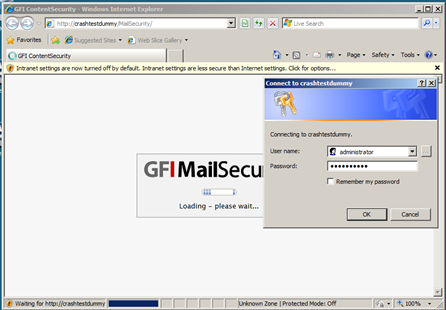
The default install will allow you to administer the product from any system with a web browser that can reach the selected site. Authenticate as a user with administrative rights to the console, as shown below
and you will be presented with the Dashboard view of the system. Here you can see green lights which indicate that all services are running, the number of any items in quarantine, and the amount of space available to the system. This dashboard has a configurable refresh rate, which is very nice for NOC displays.
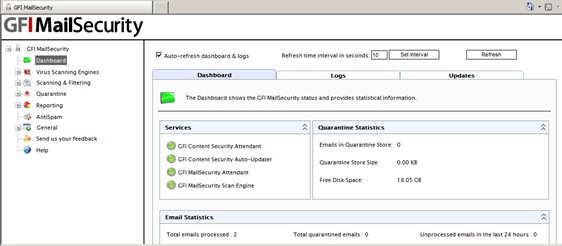
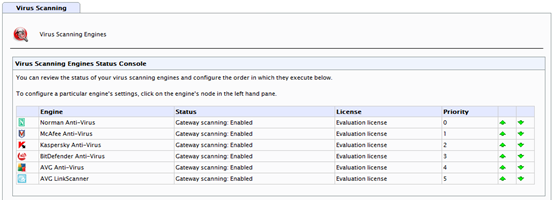
The most important aspects include the Virus Scanning Engines. Five are included: Norman, McAfee, Kaspersky, BitDefender, and AVG along with AVGs LinkScanner. You probably won’t want to use all five, and some require separate licenses, but with at least two scanning at the same time you are well protected.
From the dashboard you can also configure settings for content filtering, based on categories including adult content and offensive material, blocking of specific attachment types (like executables or media files, how to handle compressed attachments and whether or not to pass encrypted zips through), scanning for email exploits, and an HTML Sanitizer which can strip scripts; a common exploit mechanism.

Note the default shown in the screenshot. MailSecurity will scan both inbound and outbound email by default. This is part of being a responsible Netizen, and I applaud this setting.
Initial configuration
Other than selecting which virus scanners you want and tweaking any settings for attachment blocking or content filtering, there is very little required in the initial configuration. Since GFI MailSecurity uses your existing SMTP setup, the routing and delivery of emails will not be changed. You can add additional internal domains in the settings option, and you can also choose to log to a SQL server instead of the default Access database. You may also want to configure an alert address to notify an admin when content is blocked, and there are options for the storage period of quarantine files. You can even set up an RSS feed, which would enable you to check for blocked content each morning while following other feeds.
Maintenance
GFI MailSecurity can check for patches at the click of a button. All five antivirus engines will check for updates hourly by default. They will also by default email you for each successful update. You will want to turn that off pretty quickly. You will also receive an email when a failure occurs, but I didn’t receive any of these during my testing.
In summary
All in all, GFI MailSecurity is a solid product, well positioned to provide content scanning and anti-malware protection for email, with an easy to use administrative interface and low overhead. It offers good reporting out of the box, and with the optional reporting pack, it can provide any type of information management could desire.
–
Ratish Nair
MVP Exchange
Team@ MSExchangeGuru



December 31st, 2010 at 2:46 am
excellent one. never used GFI though.
Regards
Selva
December 31st, 2010 at 5:15 am
I’ll try to see how this goes. Have a staging box and a domain registered for testing.
December 31st, 2010 at 7:35 am
I use GFI and never gave me trouble. Its good to see gurus like em’ too.
Can u write something on monitoring Exchange 2007 server?
Chad M
December 31st, 2010 at 11:53 pm
Impressive one !! Glad you like GFI…
January 10th, 2011 at 6:56 am
[…] This post was mentioned on Twitter by GFI Software. GFI Software said: GFI MailSecurity – Review of a mature product for Microsoft Exchange http://ow.ly/3B0W1 […]
March 28th, 2014 at 10:31 am
Superb, what a weblog it is! This blog presents valuable facts to us,
keep it up.