Using Forefront TMG to publish Exchange ActiveSync and Outlook Web App Using Certificate Based Authentication
This is an overview on how Exchange 2010 OWA/EAS clients connect when TMG is deployed in DMZ
The following steps describe the process involved when a mobile device or Outlook Web App (OWA) connects to a mailbox using a certificate and how Kerberos Constrained Delegation and Protocol transitioning are used.
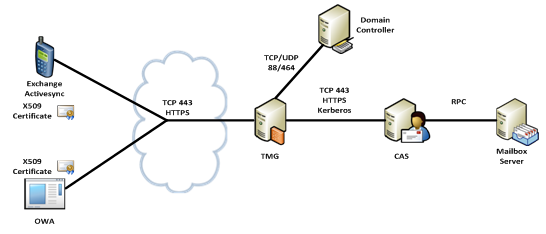
- User attempts to access mailbox using OWA or a mobile device over a cellular network. Connection between client and external TMG interface is encrypted using SSL certificate.
- TMG has been configured to publish OWA and Exchange ActiveSync URL and prompts the user for authentication.
- The user or device presents an X509 certificate as proof of identity.
-
TMG has been configured to use Kerberos Constrained Delegation (KCD) and connects to Key Distribution Center service on the Domain Controller and requests a Kerberos Ticket on behalf of the connecting user.
Note: This is where Protocol Transitioning takes place as initial user authentication method was X.509 certificate and TMG Firewall service has been configured to be allowed to request a Kerberos ticket on behalf of the user.
- The Key Distribution Center service passes back the user Kerberos Ticket to Network Service identity under which TMG Firewall is running.
- TMG has been configured to be able to delegate Kerberos tickets to an Exchange CAS server. The firewall rule on the TMG server knows the internal URL of the Exchange CAS server and passes the requested Kerberos Ticket for the authenticated user to the Exchange CAS server.
- The Exchange CAS then accesses the mailbox server where the mailbox is located, authenticating using Windows Integrated Authentication.
It is important to realize early in the planning stages of a deployment like this, that a single TMG listener cannot provide both certificate based authentication at the same time as Basic, Forms Based Authentication, or NTLM authentication. A listener can provide Forms Based Authentication with fallback to Basic, or Basic and NTLM can be used on the same listener, but certificate based authentication when used as the primary form of authentication cannot be combined with any other form of authentication.
This means it is not possible to share one external namespace/listener between clients such as Exchange ActiveSync, when it is using certificate based authentication, and Outlook Anywhere when it is using Basic Authentication. In a scenario such as this, two listeners, and therefore two namespaces and IP addresses must be used. For example, Outlook Anywhere could be configured to use mail.fabrikam.com and certificate based Exchange ActiveSync could be configured to use cert.fabrikam.com. This would require TMG to have two external facing IP addresses, two certificates (though one certificate with both names listed as SAN attributes could also be used) and two listeners.
Read more about configuring TMG/UAG with Exchange 2010 in this whitepaper
Ratish Nair
MVP Exchange
Team @MSExchangeGuru



April 30th, 2013 at 9:31 pm
Hi,
So if I want to setup TMG to publish OWA using FBA and ActiveSync using CBA, Do I just need “Integrated Auth” on the ActiveSycn VDIR, and Basic on the /OWA VDIR?, or do I need to have CBA on OWA/ActiveSync, and then another website on the CAS server for /OWA (with Basic authentication set)?
TIA
Mark
July 17th, 2016 at 4:13 pm
Hi Prabhat,
I am stuck in one of the issue which is weird. Recently deployed Exchange 2013 CU9 in environment having Exchange 2010sp3 running. I have not done switchover yet as during testing observed that when i tried to access 2013 OWA page it is working from E2k13 mailbox. But, as soon as i access E2k13 owa and enter E2k10 mailbox credential it proxy, i can see email items but not able to select anything on owa page.
Background:
OWA settings on E2k10: Fba, Basic & Windows integrated.
Owa Settings on E2k13: fba, basic & windows integrated.