Gwava Spam Guard: Enable TLS
This is a Linux box and there are few things which are not straight forward if it is not windows for a Microsoft pro. This is a hard process of a simple thing. Due to the increased requirement of security worldwide, my customer asked me to deploy TLS on their Spam Guard. This customer is using the Spam Guard name Gwava.
In the following steps, I am sharing how to install TLS cert in your Gwava server.
Creating new Cert
- We generated a Cert request in the Exchange 2013 ECP.
- Submitted the request to GoDaddy and downloaded the cert.
- Completed the request in the exchange server.
- Exported the certificate pfx file.
- Now as per the support link mentioned below, we need .crt file, .key file and a password.
http://support.gwava.com/kb/?View=entry&EntryID=2280
- We got .crt file in the download from GoDaddy.
- The challenge is how to create .key file. Then how to create the password.
Creating .key file and pass phrase
The follow steps will help in creating .key file and passphrase.
- Downloaded OpenSSL tool from here,
https://slproweb.com/download/Win32OpenSSL_Light-1_1_0c.exe
or
Check other links here
https://slproweb.com/products/Win32OpenSSL.html
- Install the OpenSSL.
-
Go to the command prompt and go to the following directory.
C:\OpenSSL-Win32\bin\
- Copy the cert.pfx in the bin folder.
-
Run the following command
openssl pkcs12 -in dec16.pfx -nocerts -out Gwava.key
Enter Import Password:
Enter PEM pass phrase:
Verifying – Enter PEM pass phrase:
- Remember the pass phrase.
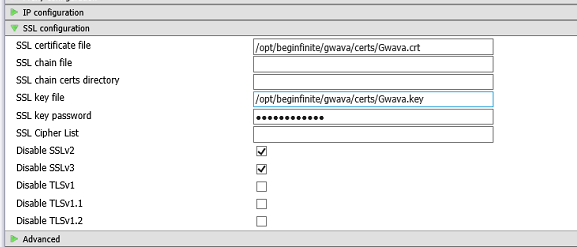
- Login to Gwava web interface, Copy the cert and enter the password.
- Click Save on the right top.
Restarting Gwava
-
Connect to Gwava using putty then Run the following command to restart the Gwava server.
RCGwavaMan Stop
RCGwavaMan Start
- Now Gwava server should be ready to accept the TLS. We can verify the verb “StartTLS” in the Ehlo output.
Additional.
We can verify if .crt and .key file matches by running the following commands and the output should match:
- C:\OpenSSL-Win32\bin>openssl x509 -noout -modulus -in Gwava.crt | openssl md5
- C:\OpenSSL-Win32\bin>openssl rsa -noout -modulus -in Gwava.key | openssl md5
Enter pass phrase for Gwava.key:
We can also verify the TLS here www.CheckTLS.com
Microsoft MVP | CTO @ Golden Five
Team@MSExchangeGuru


