Multi-Factor Authentication for RDS Portal Part1
This is a 2 blogs series in which we are explaining how to secure RDWeb with “Azure Multi-Factor Authentication”.
Previously we have explained how to install “Azure Multi-Factor Authentication” with ADFS in the following blogs:
ADFS Blogs:
https://msexchangeguru.com/2015/06/17/e2013-hybrid-part-2/
“Azure Multi-Factor Authentication” Blogs:
https://msexchangeguru.com/2017/01/16/unable-to-download-azuremfa/
https://msexchangeguru.com/2017/01/28/azure-mfa1/
https://msexchangeguru.com/2017/01/28/azure-mfa2/
We will not repeat the steps rather we would encourage to follow the above blogs.
By this time, you have understood that in most of the configurations “Azure Multi-Factor Authentication” alone does not help so most of the request goes to ADFS and ADFS forwards the Multi-Factor Authentication request to the “Azure Multi-Factor Authentication” server.
RDWeb works in the same way but RDWeb can’t forward the request by its own so we need to deploy Web Access Proxy. Web Access Proxy is actually ADFS Proxy which can be placed in the DMZ.
Step 1. Web Access Proxy installation and Configuration.
Follow this blog: https://msexchangeguru.com/2016/12/09/wap-adfs-mfa-part-1/
Step 2: Install Remote Desktop Services
- Login to the Server with the Remote Desktop server with “Domain Admins” Privileges.
- Open Server Manager
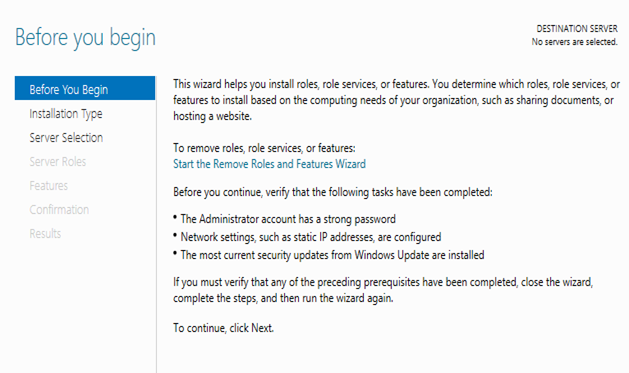
- Click on Manage and Select “Add Roles and Features”
- Click next here.
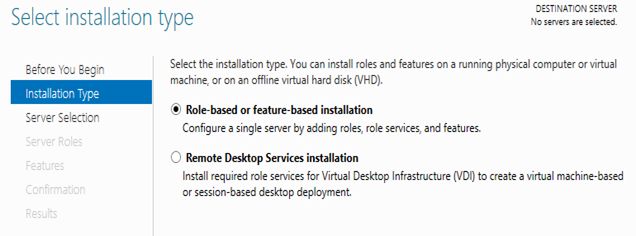
- Click next here.
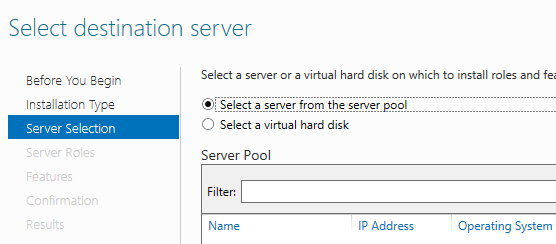
- Select the server here and click next.
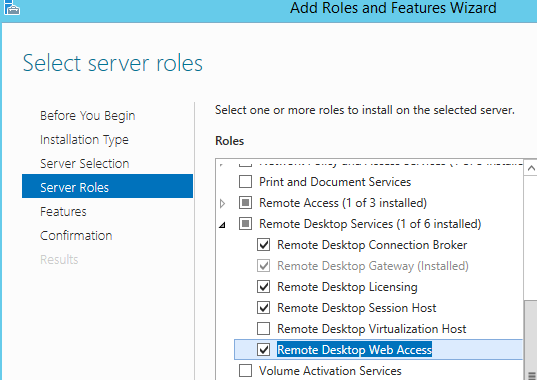
- Select the following 5 components under “Remote Desktop Services” and more components in IIS then click next.
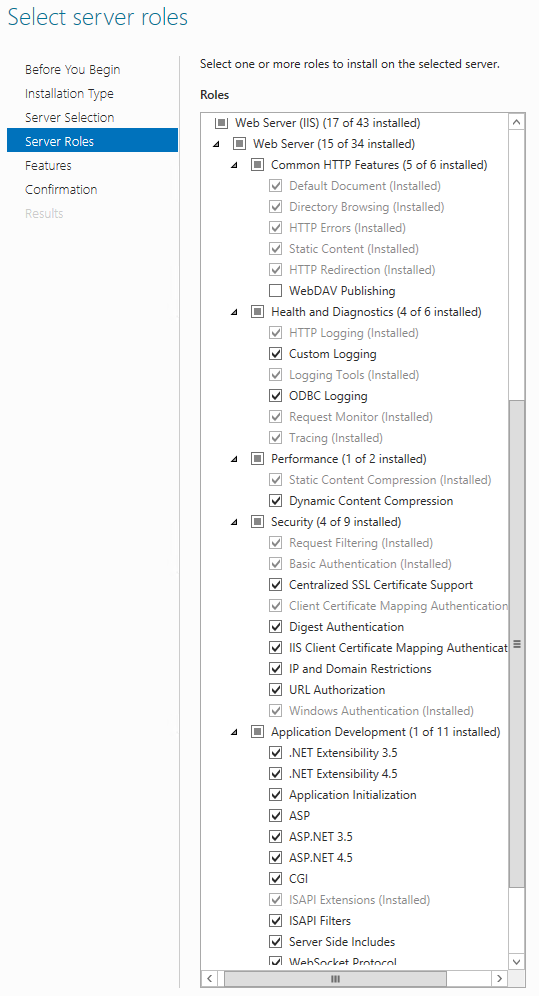
- In the features, Select Telnet Client and RPC over Http Proxy then click next.
- Click install.
- Once finish click on close.
Step 3: Create port 444. We are going to use WAP and RDWeb on the same server so we are using port 444. Hence we need to add port 444.
- Open IIS Manager
- Select “Default Web Site”
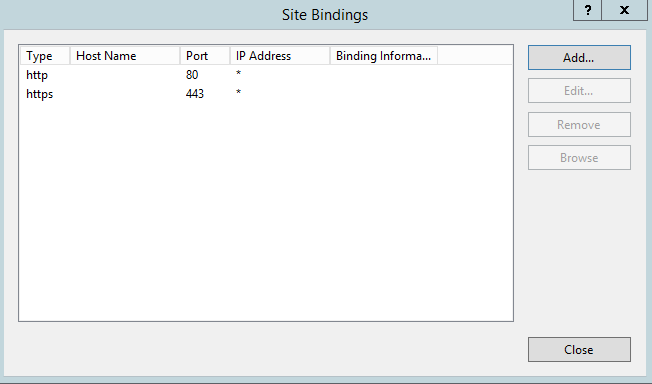
- Right click and select Bindings.
- Click on Add
- Select https, change the port to 444 and select the certificate
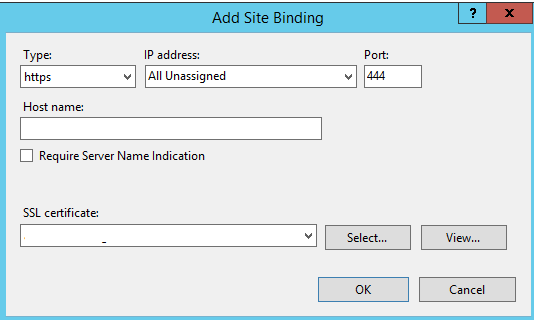
- Select the correct certificate for port 443. Then click ok and close the IIS Manager.
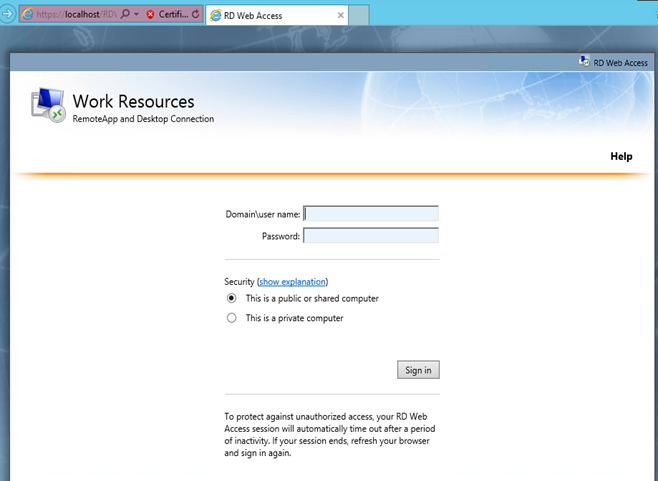
- If we browse to https://localhost/RDweb then it will open this screen.
Step4: The following blog will cover the following:
- Configure Kerberos for WAP
- Configure Delegation
- Configure ADFS Rely Trust
- Publishing the RDWeb in Web Application Proxy
- RDWEB SSO Configuration
- RDWeb Certificate configuration
https://msexchangeguru.com/2016/12/09/wap-adfs-mfa-part-2/
At this time RDWeb will start working with Multifactor Authentication.
Now we have to configure RDWeb Gateway for Multifactor Authentication using Radius server. I have explained it in Part 2.
Multi-Factor Authentication for RDS Portal Part2 – https://msexchangeguru.com/2017/02/02/mfa-for-rds2/
Microsoft MVP | CTO @ Golden Five
Team@MSExchangeGuru



February 9th, 2017 at 11:43 pm
[…] « Multi-Factor Authentication for RDS Portal Part1 Exchange Management Console error: The attempt to connect to PowerShell using […]